xhs shield 参数分析
断断续续其实拖了挺长时间的,本意是想通过亲手实践来学一下逆 app 的参数是一个怎样的流程,顺便了解下实战中涉及的安卓逆向的知识
定位 so
抓包分析
用 Reqable 对 xhs 进行抓包,翻了下请求,在请求头里看到了
shield 参数,一共 134 个字符
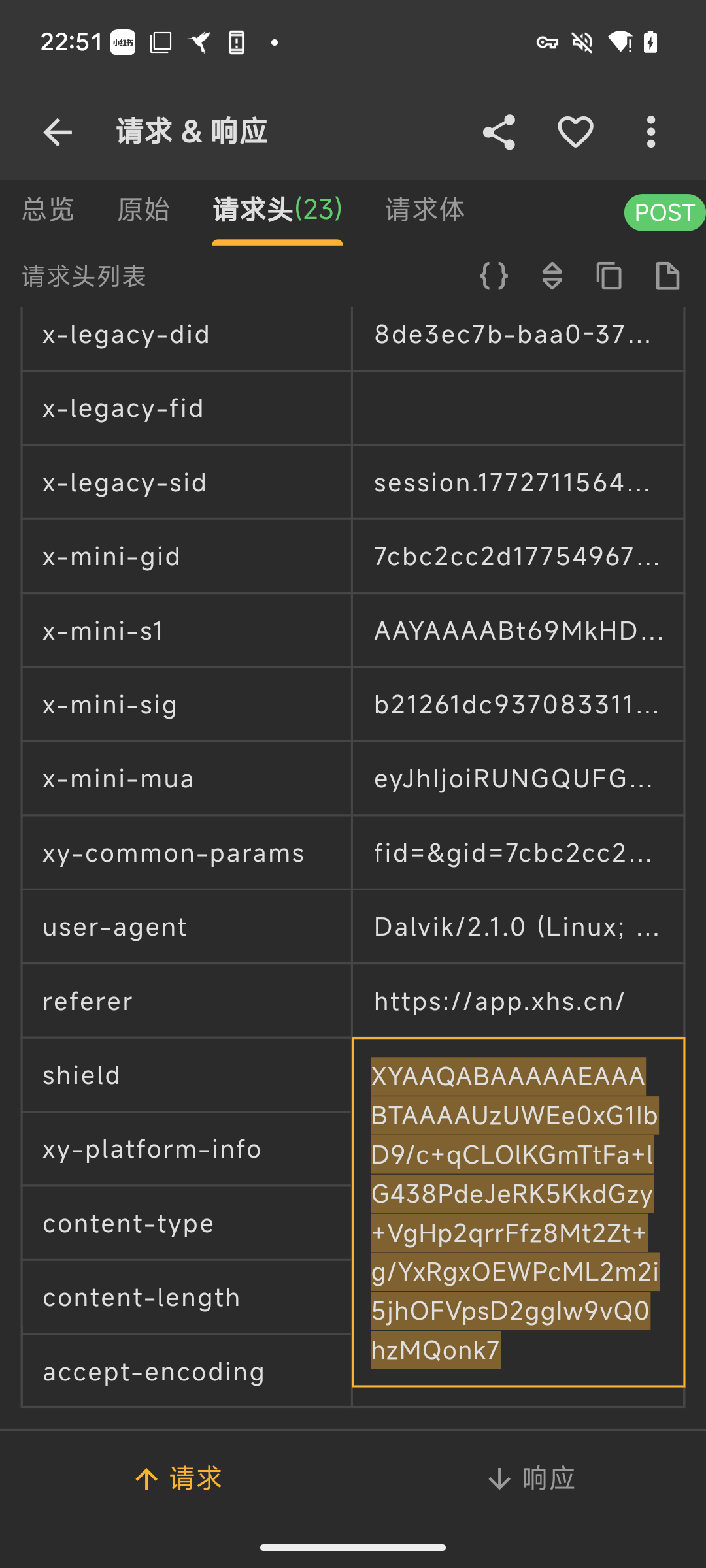
多观察几个请求头的这个参数可以发现它前 112 个字符是一样的,后面 22 个字符是变化的
hook NewStringUTF
首先需要知道这个这一串参数是从什么地方生成的,一般思路是 hook
NewStringUTF
NewStringUTF是 JNI 中的一个函数,把 native 层的const char *字符串转成 Java 层的jstring,相当于 Java/Kotlin 和 C/C++ native 代码之间的桥梁
JNI 规范里的 NewStringUTF 原型是:
1 | |
它会根据传入的 bytes 构造一个新的
java.lang.String, 并且它在 JNIEnv
函数表里的索引是 167
由此可以写出 hook NewStringUTF 的 frida 脚本
1 | |
但是尝试之后发现有 frida 检测,直接 Process terminated 了
开始以为是 frida 检测,绕了半天也没用,后面发现不是检测的问题,而是 hook 时机太早了,延后一点再注入这个就能正常看到日志了
1 | |
由此可以定位到要分析的参数在 libxyass.so 中
样本的是从 Google Play 下载的,因为谷歌推行了
Android App Bundle(.abb),按设备下发 apk,lib 在 apks 解压后的split_config.arm64_v8a.apk中
分析 so
sub_46DB0
根据 call off 的地址在 libxyass.so 中定位
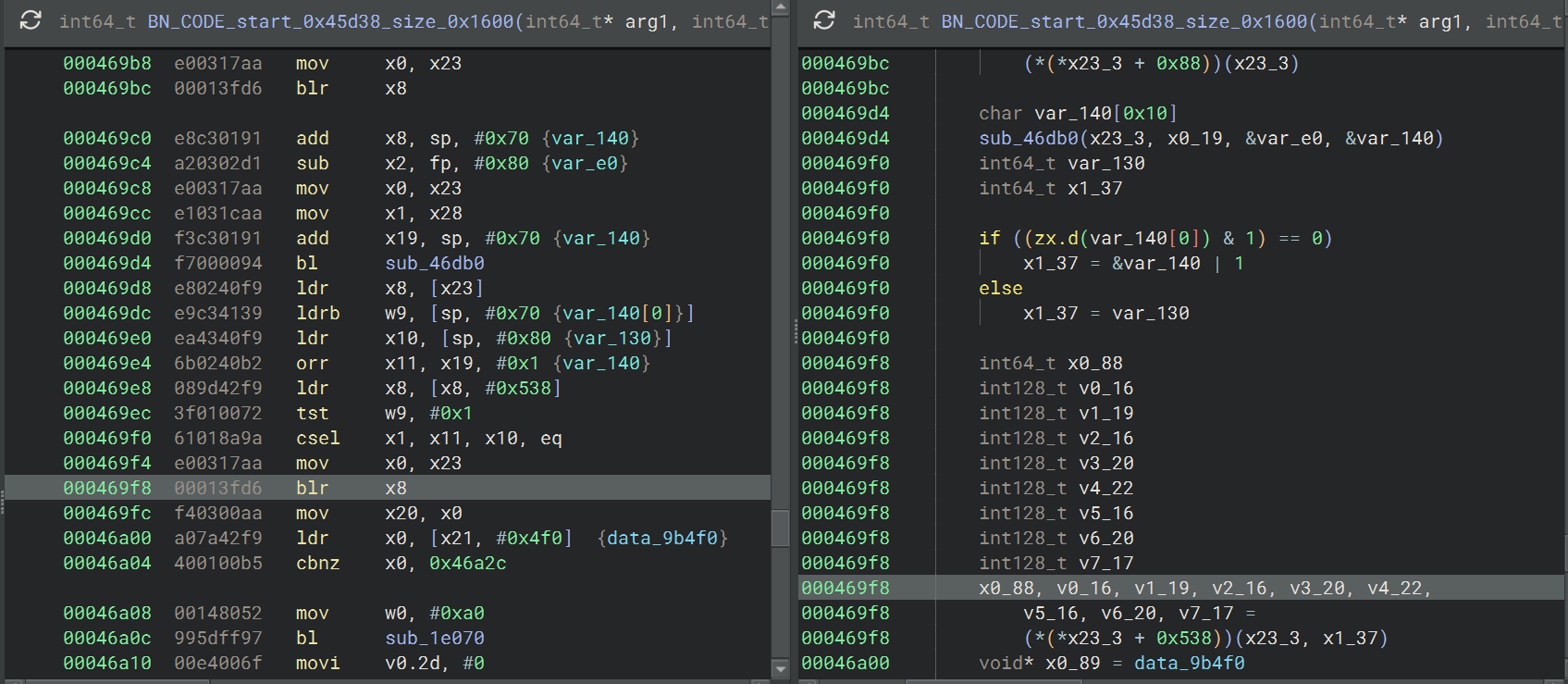
caller off 拿到的是 return address,也就是 NewStringUTF
调完之后,要返回到的下一条指令地址,想要拿到调用地址的偏移需要减去 4
字节指令长度,所以调用地址的偏移是 0x469f8
而往前看最近的函数 sub_46DB0
可能就是构造这个参数的函数了
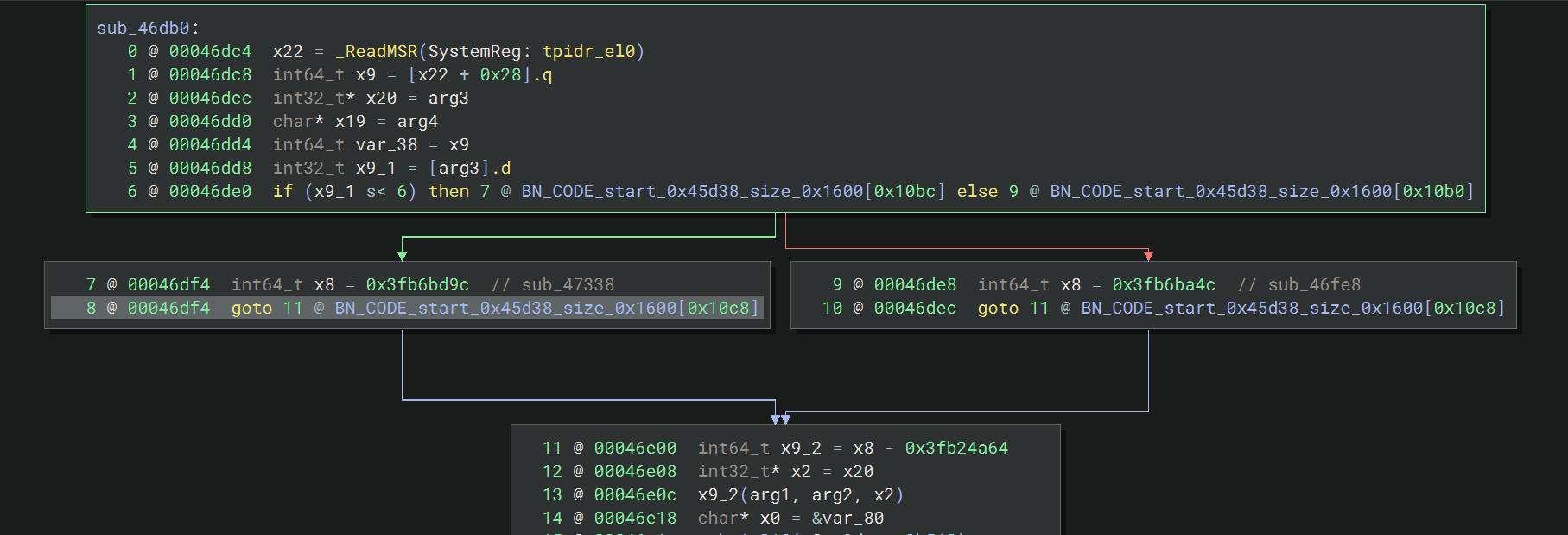
先是判断一个参数(怀疑是版本) 是否小于 6,根据结果选择
sub_47338 或者 sub_46fe8 这两个分支
hook 下 sub_46DB0 函数的参数 1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64function hook_sub_46DB0(){
const targetName = "libxyass.so";
const dlopen_ptr = Module.getGlobalExportByName("android_dlopen_ext");
if(dlopen_ptr){
Interceptor.attach(dlopen_ptr,{
onEnter:function(args){
const path = args[0]?.readUtf8String();
if (path && path.indexOf(targetName) !== -1) {
this.isTarget = true;
}
},
onLeave:function(retval){
if (this.isTarget) {
const mod = Process.findModuleByName(targetName);
if(mod){
const modBase = mod.base;
const table = modBase.add(0x976d8);
const ptr_func = table.readPointer();
const real_addr = ptr_func.sub(0x3fb24a64); // 静态计算
console.log("[+] Calculate Func Addr: " + real_addr);
Interceptor.attach(modBase.add(0x46DB0),{
onEnter:function(this:any,args){
const a1 = args[0];
const a2 = args[1];
const a3_ptr = args[2];
// const a3_var = a3_ptr.readS32();
const x8 = this.context.x8;
const x2 = this.context.x2;
console.log("\n[+] Hook sub_46DB0 args");
console.log(`[*] a1: ${a1}`);
console.log(hexdump(a1, {
length: 64,
ansi: true
}))
console.log(`[*] a2: ${a2}`);
console.log(hexdump(a2, {
length: 64,
ansi: true
}))
console.log(`[*] a3_ptr: ${a3_ptr}`);
console.log(hexdump(a3_ptr,{
length: 64,
ansi:true
}))
console.log(`[*] x8: ${x8}`);
console.log(hexdump(x8, {
length: 64,
ansi: true
}))
console.log(`[*] x2: ${x2}`);
console.log(hexdump(x2, {
length: 64,
ansi: true
}))
}
})
}
}
}
})
}
}
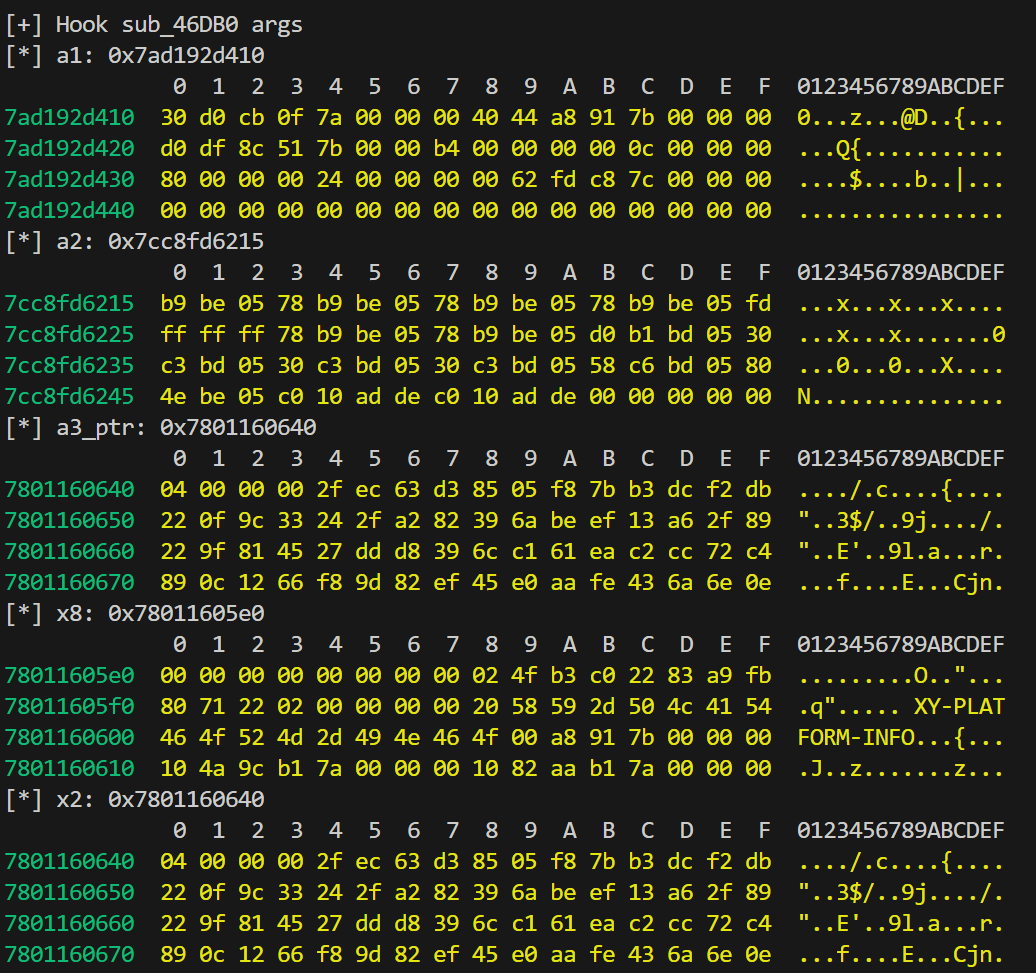
从 arg3 指向的地址处看到第一个字节是 0x4,4 < 6, 所以走的是
sub_47338 分支
1 | |
sub_4b8c8(RC4 + Base64)
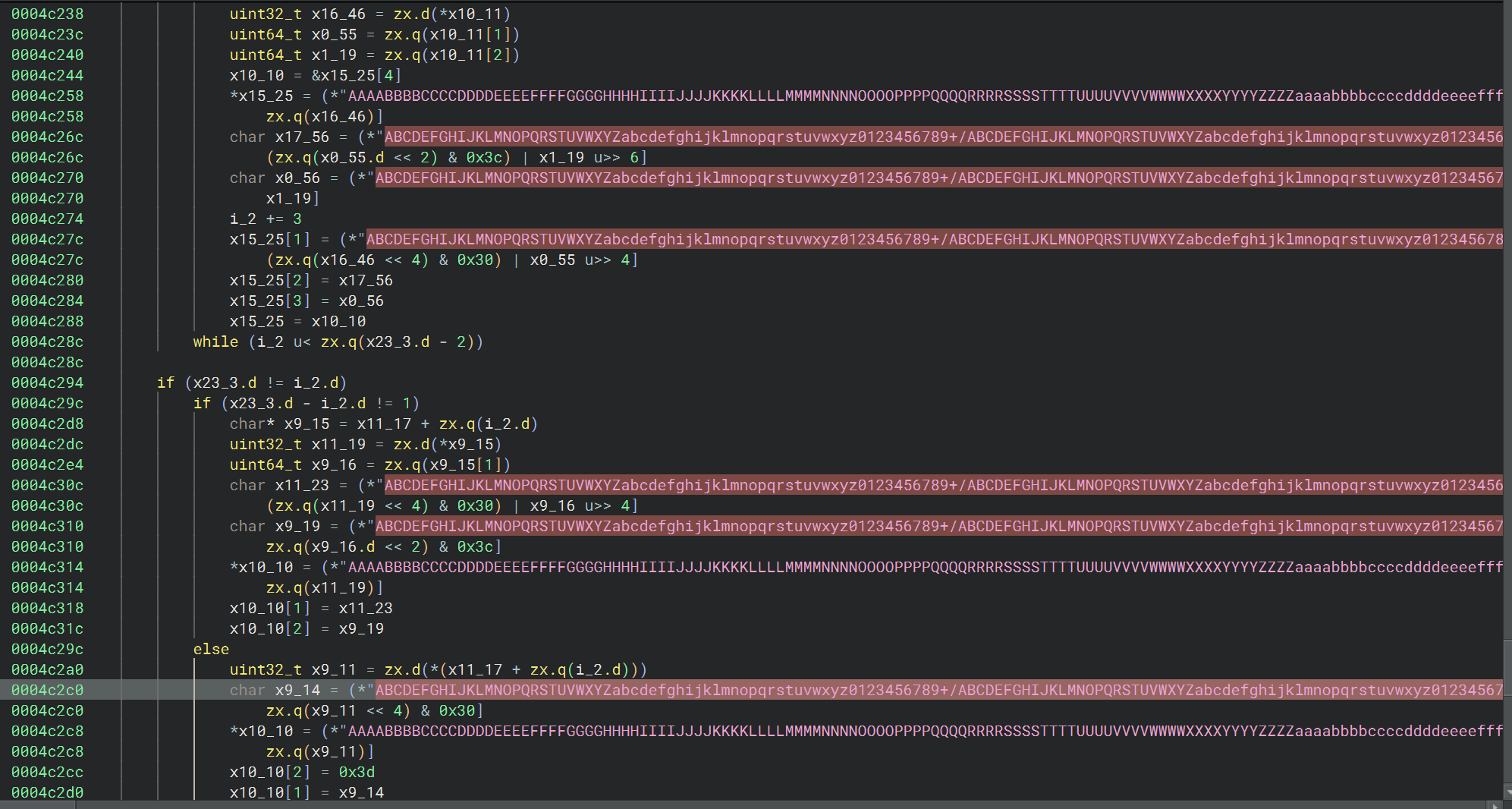
Base64
可以看到这个函数有很多个参数并且最后面有个明显的 base64
算输出长度
Base64 字符表
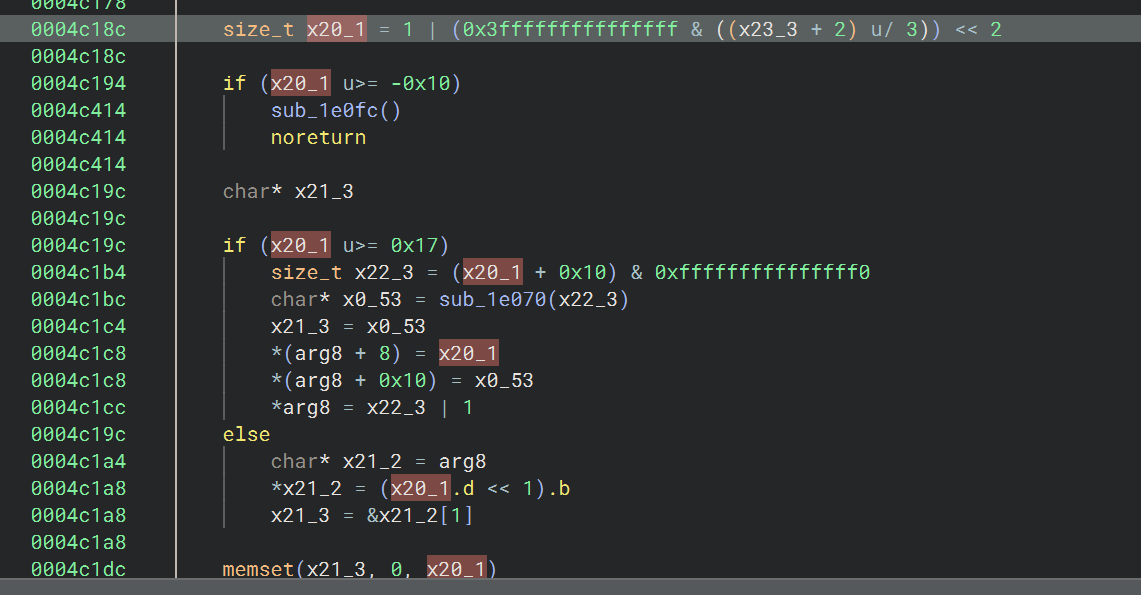
sub_1e3c8
sub_4b8c8 中多次调用的这个函数
1 | |
arg1:目标字符串对象,arg2:要追加的数据地址,arg3:要追加的数据长度
先判断 arg1 当前是短模式还是长模式,取出当前长度 size
和当前容量 capacity,判断剩余容量够不够追加 arg3
字节,够的话直接把 arg2 指向的数据复制到末尾,不够的话调用
sub_1e1d4 做扩容并追加,然后更新长度字段,在新末尾补
'\0',返回 arg1
就是 append string 的逻辑
sub_1e070
1 | |
相当于 C++ 里的 operator new(size_t) / allocator
的底层分配函数
sub_1e494
1 | |
从位置 arg2 开始删除最多 arg3
个字符,并维护结尾 \0
结合反编译先 hook 一下参数 1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85function hook_sub_4B8C8(){
const targetName = "libxyass.so";
const dlopen_ptr = Module.getGlobalExportByName("android_dlopen_ext");
if(dlopen_ptr){
Interceptor.attach(dlopen_ptr,{
onEnter:function(args){
const path = args[0]?.readUtf8String();
if (path && path.indexOf(targetName) !== -1) {
this.isTarget = true;
}
},
onLeave:function(retval){
if (this.isTarget) {
const mod = Process.findModuleByName(targetName);
if(mod){
let modBase = mod.base;
let funcAddr = modBase.add(0x4B8C8);
Interceptor.attach(funcAddr,{
onEnter:function(args){
console.log("\n");
console.log("[*] a1 = " + args[0]?.toInt32());
console.log(
"[*] a2 =\n" +
hexdump(args[1]!, {
length: 64,
ansi: true
})
);
console.log("[*] a3 = " + args[2]?.toInt32());
console.log("[*] a4 = " + args[3]?.toInt32());
console.log(
"[*] a5 =\n" +
hexdump(args[4]!, {
length: 64,
ansi: true
})
);
console.log(
"[*] a6 =\n" +
hexdump(args[5]!, {
length: args[6]!.toUInt32(),
ansi: true
})
);
console.log("[*] a7 = " + args[6]!.toInt32());
}
})
}
}
}
})
}
}
function getStdStringInfo(ptr: NativePointer) {
if (ptr.isNull() || ptr.toUInt32() < 0x1000) {
return { size: 0, data: ptr };
}
try {
const firstByte = ptr.readU8();
let size: number;
let dataPtr: NativePointer;
if ((firstByte & 1) === 0) {
// 短模式
size = firstByte >> 1;
dataPtr = ptr.add(1);
} else {
// 长模式
size = ptr.add(8).readU64().toNumber();
dataPtr = ptr.add(16).readPointer();
}
if (size > 100000) return { size: 0, data: ptr };
return { size: size, data: dataPtr };
} catch (e) {
return { size: 0, data: ptr };
}
}
部分日志如下 1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61[*] a1 = 1
[*] a2 =
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
76ec8ba700 0e 39 31 39 33 38 30 33 00 00 00 00 00 00 00 00 .9193803........
76ec8ba710 50 1e eb ed 79 00 00 00 10 a7 8b ec 76 00 00 00 P...y.......v...
76ec8ba720 e0 a6 8b ec 76 00 00 00 d8 ff ff ff 80 ff ff ff ....v...........
76ec8ba730 20 f1 7a d0 39 5d af 75 77 b9 fe 9d 1a 64 6e 63 .z.9].uw....dnc
[*] a3 = -319115519
[*] a4 = 4
[*] a5 =
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
76ec8ba6e8 31 00 00 00 00 00 00 00 24 00 00 00 00 00 00 00 1.......$.......
76ec8ba6f8 50 90 ed ed 79 00 00 00 0e 39 31 39 33 38 30 33 P...y....9193803
76ec8ba708 00 00 00 00 00 00 00 00 50 1e eb ed 79 00 00 00 ........P...y...
76ec8ba718 10 a7 8b ec 76 00 00 00 e0 a6 8b ec 76 00 00 00 ....v.......v...
[*] a6 =
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
76ec8ba731 f1 7a d0 39 5d af 75 77 b9 fe 9d 1a 64 6e 63 5c .z.9].uw....dnc\
[*] a7 = 16
[*] a1 = 1
[*] a2 =
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
76aa228550 0e 39 31 39 33 38 30 33 00 00 00 00 00 00 00 00 .9193803........
76aa228560 50 1e eb ed 79 00 00 00 60 85 22 aa 76 00 00 00 P...y...`.".v...
76aa228570 30 85 22 aa 76 00 00 00 d8 ff ff ff 80 ff ff ff 0.".v...........
76aa228580 20 f6 e1 5f 18 eb 36 e5 9c 36 13 3e e9 22 be eb .._..6..6.>."..
[*] a3 = -319115519
[*] a4 = 4
[*] a5 =
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
76aa228538 31 00 00 00 00 00 00 00 24 00 00 00 00 00 00 00 1.......$.......
76aa228548 90 59 f4 ed 79 00 00 00 0e 39 31 39 33 38 30 33 .Y..y....9193803
76aa228558 00 00 00 00 00 00 00 00 50 1e eb ed 79 00 00 00 ........P...y...
76aa228568 60 85 22 aa 76 00 00 00 30 85 22 aa 76 00 00 00 `.".v...0.".v...
[*] a6 =
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
76aa228581 f6 e1 5f 18 eb 36 e5 9c 36 13 3e e9 22 be eb 1d .._..6..6.>."...
[*] a7 = 16
[*] a1 = 1
[*] a2 =
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
77ac5305c0 0e 39 31 39 33 38 30 33 00 00 00 00 00 00 00 00 .9193803........
77ac5305d0 50 1e eb ed 79 00 00 00 d0 05 53 ac 77 00 00 00 P...y.....S.w...
77ac5305e0 a0 05 53 ac 77 00 00 00 d8 ff ff ff 80 ff ff ff ..S.w...........
77ac5305f0 20 17 ff 6a 49 ac 2c 90 dd 49 5e 5d 59 2b 8e 16 ..jI.,..I^]Y+..
[*] a3 = -319115519
[*] a4 = 4
[*] a5 =
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
77ac5305a8 31 00 00 00 00 00 00 00 24 00 00 00 00 00 00 00 1.......$.......
77ac5305b8 90 59 f4 ed 79 00 00 00 0e 39 31 39 33 38 30 33 .Y..y....9193803
77ac5305c8 00 00 00 00 00 00 00 00 50 1e eb ed 79 00 00 00 ........P...y...
77ac5305d8 d0 05 53 ac 77 00 00 00 a0 05 53 ac 77 00 00 00 ..S.w.....S.w...
[*] a6 =
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
77ac5305f1 17 ff 6a 49 ac 2c 90 dd 49 5e 5d 59 2b 8e 16 a6 ..jI.,..I^]Y+...
[*] a7 = 16
9193803 是版本号,a7 恒为 16,推测为 a6 的长度,a6 的 16
字节没什么规律,应该是经过某个加密后的数据
结合 ai 分析修缮了下 hook 脚本,把返回值顺便也 hook 出来
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153function hook_sub_4B8C8_v2() {
const targetName = "libxyass.so";
const mod = Process.findModuleByName(targetName);
if (mod) {
attach_to_func(mod.base);
} else {
const dlopen_ptr = Module.getGlobalExportByName("android_dlopen_ext");
if (dlopen_ptr) {
Interceptor.attach(dlopen_ptr, {
onEnter: function (args) {
this.path = args[0]?.readUtf8String();
},
onLeave: function (retval) {
if (this.path && this.path.indexOf(targetName) !== -1) {
const m = Process.findModuleByName(targetName);
if (m) attach_to_func(m.base);
}
}
});
}
}
}
interface StdStringInfo {
size: number;
data: NativePointer;
content: string | null;
}
function attach_to_func(modBase: NativePointer) {
const funcAddr = modBase.add(0x4B8C8);
console.log("[+] Hooking sub_4B8C8 at: " + funcAddr);
Interceptor.attach(funcAddr, {
onEnter: function (args) {
const a1 = args[0].toInt32();
const a3 = args[2].toInt32();
const a4 = args[3].toInt32();
const a7 = args[6].toInt32();
// 解析 std::string
const str2 = getStdString(args[1]);
const str5 = getStdString(args[4]);
// this.arg8_ptr = this.context.x8;
this.arg8_ptr = (this.context as any).x8;
if (this.arg8_ptr.toUInt32() < 0x1000) {
this.arg8_ptr = args[7];
}
console.log("\n" + "=".repeat(40));
console.log("[*] Call sub_4B8C8 ");
console.log(`[+] arg1 (ID): ${a1} (Hex: 0x${a1.toString(16).padStart(8, '0')})`);
console.log(`[+] arg3 (Serial): ${a3}`);
console.log(`[+] arg4 (Type): ${a4} -> 转换为 Header 中的: ${a4 != 0 ? 2 : 1}`);
console.log(`[+] arg2 (String 1):`);
console.log(` - Len: ${str2.size}`);
console.log(` - Content: ${str2.content}`);
if (str2.size > 0) {
console.log(hexdump(str2.data, { length: str2.size, ansi: true }));
}
console.log(`[+] arg5 (String 2):`);
console.log(` - Len: ${str5.size}`);
console.log(` - Content: ${str5.content}`);
if (str5.size > 0) {
console.log(hexdump(str5.data, { length: str5.size, ansi: true }));
}
console.log(`[+] arg6 (Raw Data):`);
console.log(` - Len (arg7): ${a7}`);
if (a7 > 0 && !args[5].isNull()) {
console.log(hexdump(args[5], { length: a7, ansi: true }));
}
console.log("=".repeat(40));
},
onLeave: function (retval) {
const result = getStdString(this.arg8_ptr);
console.log("\n[!] sub_4B8C8 Return:");
if (result.size > 0) {
console.log(`[*] Result Content: ${result.content}`);
} else {
console.log("[*] Result is empty");
}
}
});
}
function getStdStringInfo(ptr: NativePointer) {
if (ptr.isNull() || ptr.toUInt32() < 0x1000) {
return { size: 0, data: ptr };
}
try {
const firstByte = ptr.readU8();
let size: number;
let dataPtr: NativePointer;
if ((firstByte & 1) === 0) {
// 短模式
size = firstByte >> 1;
dataPtr = ptr.add(1);
} else {
// 长模式
size = ptr.add(8).readU64().toNumber();
dataPtr = ptr.add(16).readPointer();
}
if (size > 100000) return { size: 0, data: ptr };
return { size: size, data: dataPtr };
} catch (e) {
return { size: 0, data: ptr };
}
}
function getStdString(ptr: NativePointer): StdStringInfo {
if (ptr.isNull() || ptr.toUInt32() < 0x1000) {
return { size: 0, data: ptr, content: null };
}
try {
const firstByte = ptr.readU8();
let size: number;
let dataPtr: NativePointer;
if ((firstByte & 1) === 0) {
// 短模式 (SSO)
size = firstByte >> 1;
dataPtr = ptr.add(1);
} else {
// 长模式
size = ptr.add(8).readU64().toNumber();
dataPtr = ptr.add(16).readPointer();
}
let content: string | null = null;
if (size > 0) {
try {
content = dataPtr.readUtf8String(size);
} catch (e) {
content = "[Binary/Non-UTF8 Data]";
}
} else {
content = "";
}
return { size, data: dataPtr, content: content };
} catch (e) {
return { size: 0, data: ptr, content: "[Error Reading]" };
}
}
1 | |
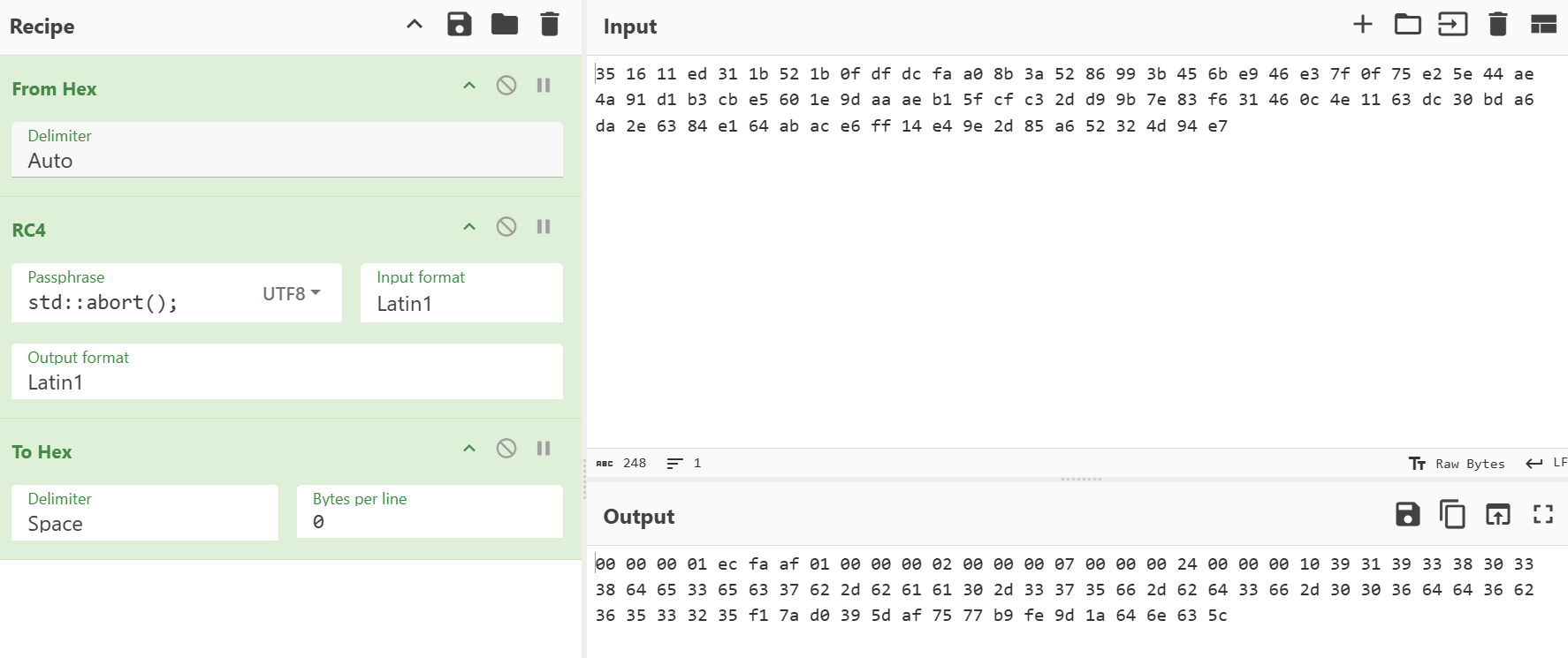
RC4
中间部分很像 RC4
初始化 256 字节状态表
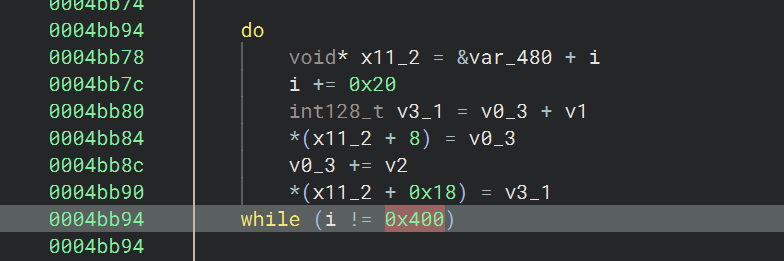
之后是 KSA ,key 为 std::abort();
这个 key 通过 frida hook 也能验证
1 | |
hook 结果
1 | |
后面的循环则是 PRGA + XOR 输出,在循环里面更新索引,从状态表取值,swap,再取一个字节与明文异或
hook append 函数(sub_1e3c8)
这个 hook 确实是挺重要的一个 hook,很多推测和验证都是根据这个 hook 拿到的数据来分析的
1 | |
这是其中一轮的日志 1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126[+] === sub_1E3C8 ===
[*] SIZE before append: 24
[*] CONTENT before append:
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
7a9dec8a90 00 00 00 01 ec fa af 01 00 00 00 02 00 00 00 07 ................
7a9dec8aa0 00 00 00 24 00 00 00 10 ...$....
[*] appending length: 7
[*] Data to Append:
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
76fbf88701 39 31 39 33 38 30 33 9193803
[*] SIZE after append: 31
[*] CONTENT after append:
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
7a9dec8a90 00 00 00 01 ec fa af 01 00 00 00 02 00 00 00 07 ................
7a9dec8aa0 00 00 00 24 00 00 00 10 39 31 39 33 38 30 33 ...$....9193803
[+] Data Flow into sub_1E3C8 (Call 2)
[*] Length: 36
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
79edecb610 38 64 65 33 65 63 37 62 2d 62 61 61 30 2d 33 37 8de3ec7b-baa0-37
79edecb620 35 66 2d 62 64 33 66 2d 30 30 36 64 64 36 62 36 5f-bd3f-006dd6b6
79edecb630 35 33 32 35 5325
[+] === sub_1E3C8 ===
[*] SIZE before append: 31
[*] CONTENT before append:
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
7a9dec8a90 00 00 00 01 ec fa af 01 00 00 00 02 00 00 00 07 ................
7a9dec8aa0 00 00 00 24 00 00 00 10 39 31 39 33 38 30 33 ...$....9193803
[*] appending length: 36
[*] Data to Append:
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
79edecb610 38 64 65 33 65 63 37 62 2d 62 61 61 30 2d 33 37 8de3ec7b-baa0-37
79edecb620 35 66 2d 62 64 33 66 2d 30 30 36 64 64 36 62 36 5f-bd3f-006dd6b6
79edecb630 35 33 32 35 5325
[*] SIZE after append: 67
[*] CONTENT after append:
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
790de3a430 00 00 00 01 ec fa af 01 00 00 00 02 00 00 00 07 ................
790de3a440 00 00 00 24 00 00 00 10 39 31 39 33 38 30 33 38 ...$....91938038
790de3a450 64 65 33 65 63 37 62 2d 62 61 61 30 2d 33 37 35 de3ec7b-baa0-375
790de3a460 66 2d 62 64 33 66 2d 30 30 36 64 64 36 62 36 35 f-bd3f-006dd6b65
790de3a470 33 32 35 325
[+] Data Flow into sub_1E3C8 (Call 3)
[*] Length: 16
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
76fbf881e9 f1 7a d0 39 5d af 75 77 b9 fe 9d 1a 64 6e 63 5c .z.9].uw....dnc\
[+] === sub_1E3C8 ===
[*] SIZE before append: 67
[*] CONTENT before append:
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
790de3a430 00 00 00 01 ec fa af 01 00 00 00 02 00 00 00 07 ................
790de3a440 00 00 00 24 00 00 00 10 39 31 39 33 38 30 33 38 ...$....91938038
790de3a450 64 65 33 65 63 37 62 2d 62 61 61 30 2d 33 37 35 de3ec7b-baa0-375
790de3a460 66 2d 62 64 33 66 2d 30 30 36 64 64 36 62 36 35 f-bd3f-006dd6b65
790de3a470 33 32 35 325
[*] appending length: 16
[*] Data to Append:
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
76fbf881e9 f1 7a d0 39 5d af 75 77 b9 fe 9d 1a 64 6e 63 5c .z.9].uw....dnc\
[*] SIZE after append: 83
[*] CONTENT after append:
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
796df98aa0 00 00 00 01 ec fa af 01 00 00 00 02 00 00 00 07 ................
796df98ab0 00 00 00 24 00 00 00 10 39 31 39 33 38 30 33 38 ...$....91938038
796df98ac0 64 65 33 65 63 37 62 2d 62 61 61 30 2d 33 37 35 de3ec7b-baa0-375
796df98ad0 66 2d 62 64 33 66 2d 30 30 36 64 64 36 62 36 35 f-bd3f-006dd6b65
796df98ae0 33 32 35 f1 7a d0 39 5d af 75 77 b9 fe 9d 1a 64 325.z.9].uw....d
796df98af0 6e 63 5c nc\
=== RC4 Start ===
[*] Length: 83
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
76fbf88241 00 00 00 00 00 00 00 53 00 00 00 00 00 00 00 a0 .......S........
76fbf88251 8a f9 6d 79 00 00 00 80 00 00 00 33 98 27 cd 00 ..my.......3.'..
76fbf88261 00 00 00 00 00 00 00 7c 00 00 00 2e 00 00 00 0e .......|........
76fbf88271 00 00 00 3d 00 00 00 09 00 00 00 32 00 00 00 e3 ...=.......2....
[!!!] CRITICAL: Final Binary Packet before Base64
[*] Length: 83
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
7abde540b0 35 16 11 ed 31 1b 52 1b 0f df dc fa a0 8b 3a 52 5...1.R.......:R
7abde540c0 86 99 3b 45 6b e9 46 e3 7f 0f 75 e2 5e 44 ae 4a ..;Ek.F...u.^D.J
7abde540d0 91 d1 b3 cb e5 60 1e 9d aa ae b1 5f cf c3 2d d9 .....`....._..-.
7abde540e0 9b 7e 83 f6 31 46 0c 4e 11 63 dc 30 bd a6 da 2e .~..1F.N.c.0....
7abde540f0 63 84 e1 64 ab ac e6 ff 14 e4 9e 2d 85 a6 52 32 c..d.......-..R2
7abde54100 4d 94 e7 M..
[+] Data Flow into sub_1E3C8 (Call 4)
[*] Length: 83
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
7abde540b0 35 16 11 ed 31 1b 52 1b 0f df dc fa a0 8b 3a 52 5...1.R.......:R
7abde540c0 86 99 3b 45 6b e9 46 e3 7f 0f 75 e2 5e 44 ae 4a ..;Ek.F...u.^D.J
7abde540d0 91 d1 b3 cb e5 60 1e 9d aa ae b1 5f cf c3 2d d9 .....`....._..-.
7abde540e0 9b 7e 83 f6 31 46 0c 4e 11 63 dc 30 bd a6 da 2e .~..1F.N.c.0....
7abde540f0 63 84 e1 64 ab ac e6 ff 14 e4 9e 2d 85 a6 52 32 c..d.......-..R2
7abde54100 4d 94 e7 M..
[+] === sub_1E3C8 ===
[*] SIZE before append: 16
[*] CONTENT before append:
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
76fbf881e9 00 04 00 04 00 00 00 01 00 00 00 53 00 00 00 53 ...........S...S
[*] appending length: 83
[*] Data to Append:
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
7abde540b0 35 16 11 ed 31 1b 52 1b 0f df dc fa a0 8b 3a 52 5...1.R.......:R
7abde540c0 86 99 3b 45 6b e9 46 e3 7f 0f 75 e2 5e 44 ae 4a ..;Ek.F...u.^D.J
7abde540d0 91 d1 b3 cb e5 60 1e 9d aa ae b1 5f cf c3 2d d9 .....`....._..-.
7abde540e0 9b 7e 83 f6 31 46 0c 4e 11 63 dc 30 bd a6 da 2e .~..1F.N.c.0....
7abde540f0 63 84 e1 64 ab ac e6 ff 14 e4 9e 2d 85 a6 52 32 c..d.......-..R2
7abde54100 4d 94 e7 M..
[*] SIZE after append: 99
[*] CONTENT after append:
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
7a8df3d1e0 00 04 00 04 00 00 00 01 00 00 00 53 00 00 00 53 ...........S...S
7a8df3d1f0 35 16 11 ed 31 1b 52 1b 0f df dc fa a0 8b 3a 52 5...1.R.......:R
7a8df3d200 86 99 3b 45 6b e9 46 e3 7f 0f 75 e2 5e 44 ae 4a ..;Ek.F...u.^D.J
7a8df3d210 91 d1 b3 cb e5 60 1e 9d aa ae b1 5f cf c3 2d d9 .....`....._..-.
7a8df3d220 9b 7e 83 f6 31 46 0c 4e 11 63 dc 30 bd a6 da 2e .~..1F.N.c.0....
7a8df3d230 63 84 e1 64 ab ac e6 ff 14 e4 9e 2d 85 a6 52 32 c..d.......-..R2
7a8df3d240 4d 94 e7 M..
=== Base64 output ===
AAQABAAAAAEAAABTAAAAUzUWEe0xG1IbD9/c+qCLOlKGmTtFa+lG438PdeJeRK5KkdGzy+VgHp2qrrFfz8Mt2Zt+g/YxRgxOEWPcML2m2i5jhOFkq6zm/xTkni2FplIyTZTn
根据这个结果可以看出,它先加载了 24 字节的数据,接着是版本号
9193803,然后是一个 UUID
8de3ec7b-baa0-375f-bd3f-006dd6b65325,最后是 16
字节的加密数据,到这里一共有 83 字节的数据,经过了 RC4
加密,加密后又追加了 16 字节的数据,最后对 99 字节的数据进行了 Base64
编码
并且可以验证这个 RC4 是标准的
观察多轮结果可以发现 RC4 结束后 append 的那 16 字节数据是固定的
00 04 00 04 00 00 00 01 00 00 00 53 00 00 00 53,变化的是进入
RC4 加密前的 16 字节
而对于最开始加载的 24 字节的 Header 其实是与参数相对应的
00 00 00 01 是 arg1 的大端表示
ec fa af 01 是 arg3 的大端表示

00 00 00 02
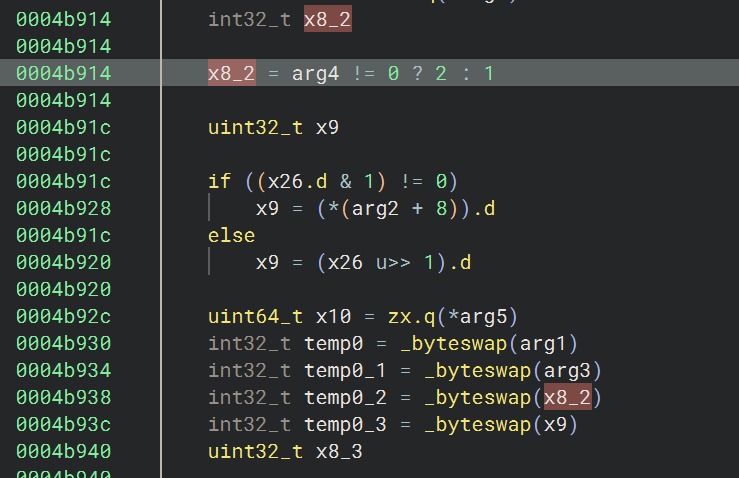
arg4 != 0 所以转换为 Header 中的 2
00 00 00 07 是 arg2 的长度(即版本号字符串 9193803
的长度)
00 00 00 24 是 arg5 的长度(即 UUID 字符串的长度)
00 00 00 10 是 arg6 的长度
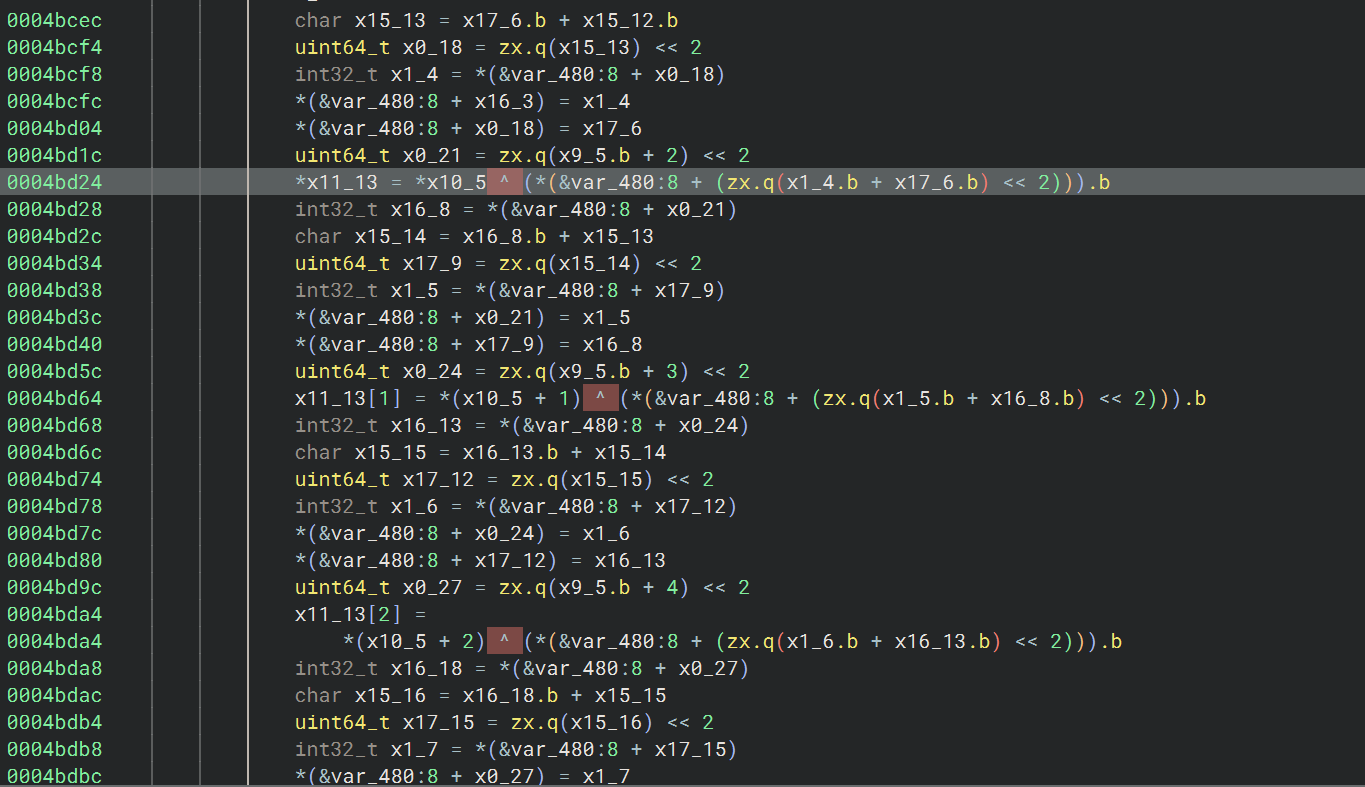
sub_47338
分析这条链路的时候,有很多 br 间接跳转和混淆
把 Sections 中的 .data
由默认的可写改为只读,这样能解决一部分简单的间接跳转,bn
可以自动分析出来跳转地址
另外的间接跳转则要根据不同情况进行分析
1 | |
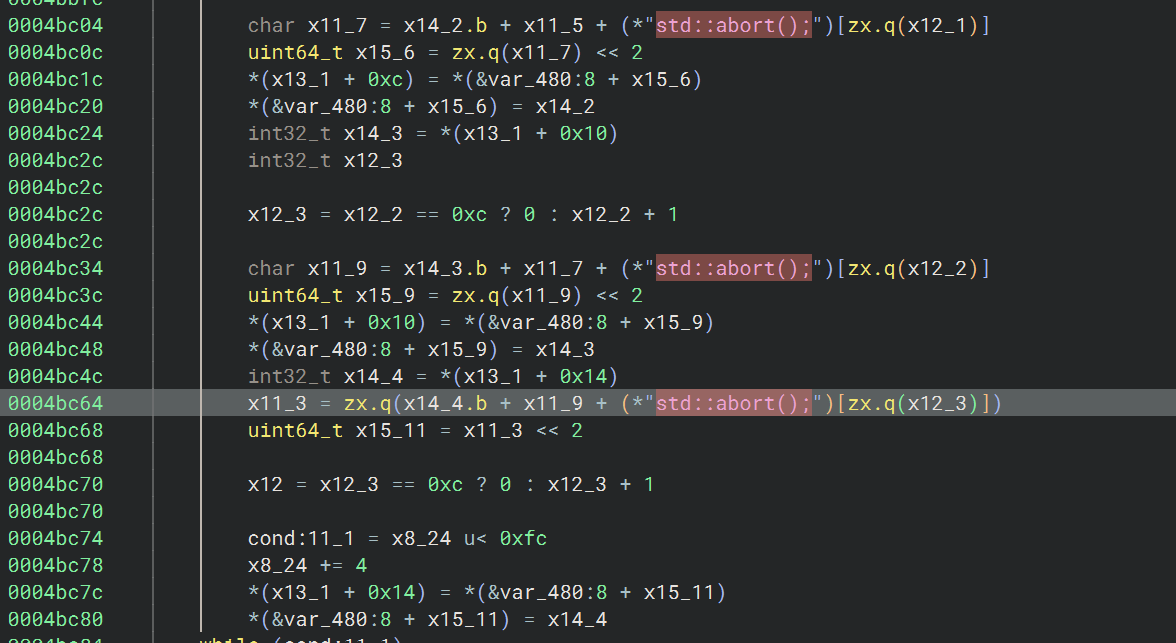
sub_850d8
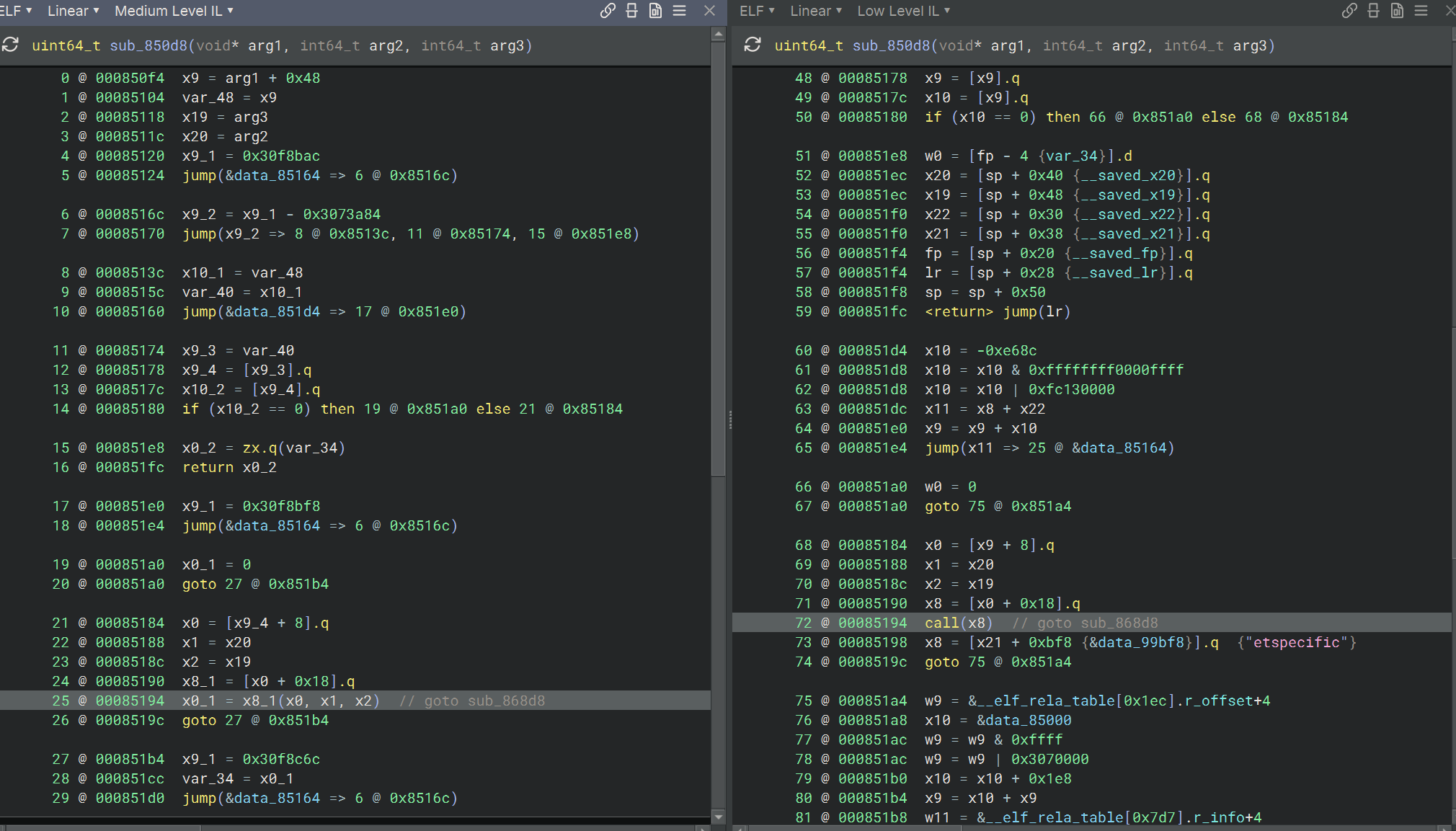
虚函数调用,frida hook 或者 trace 的方式可以获取到 vtable 和函数地址,得到的 0x85194 处调用的 function_offset 是 0x868d8,所以是 sub_868d8(x0, arg2, arg3)
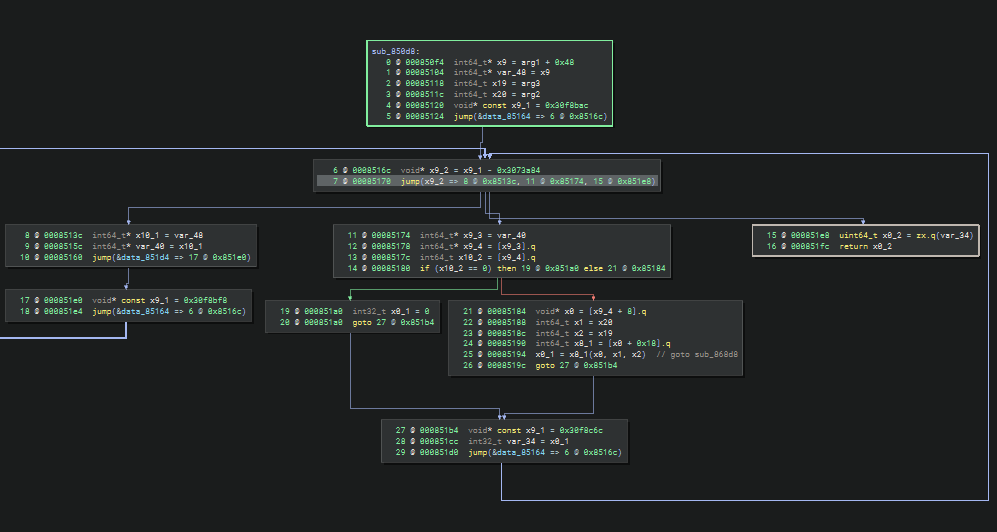
同时这个函数也是一个小型的控制流平坦化,分发器通过 x9_2
的值来决定下一步执行的基本块
sub_868a8
0x868d8 跳转过去实际是在 sub_868a8 这个函数里面
1 | |
很像是一个 hash update 的函数 Update(ctx, data, len)
根据反编译函数签名可以分析为
sub_868a8(ctx_wrapper* arg1, const uint8_t* data, size_t len)
arg1 是 外层对象, *(arg1 + 0x10) 是 hash
context 结构体,arg2 是输入数据指针,arg3
是输入长度
sub_86e44
sub_89240
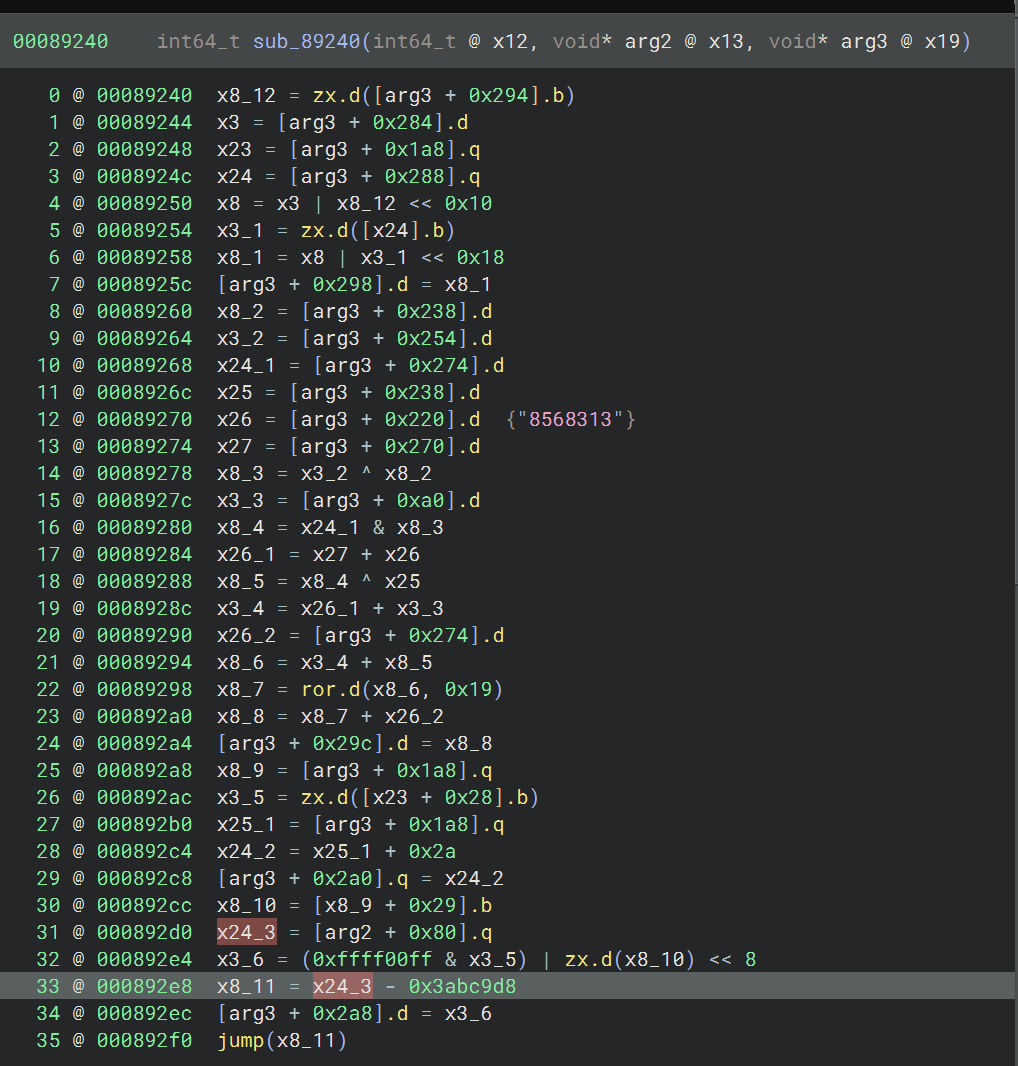
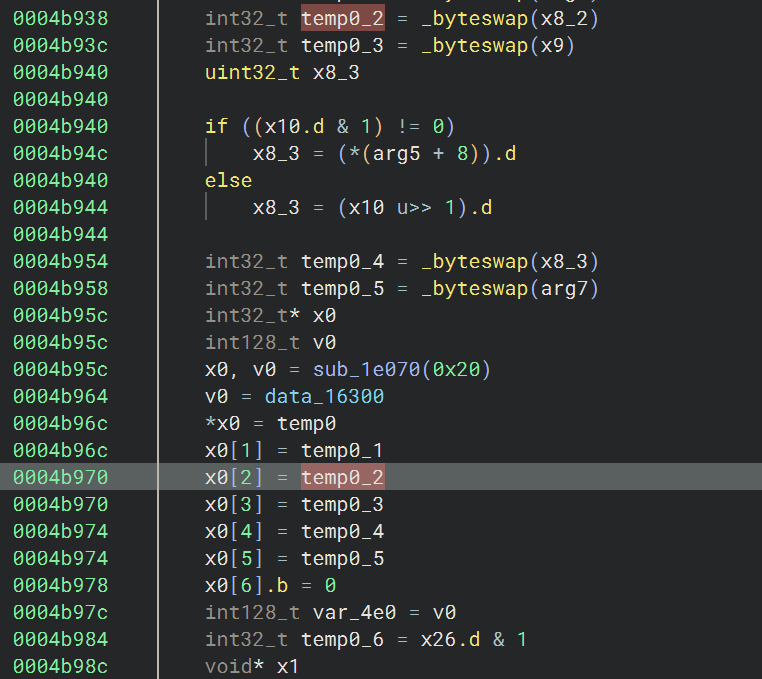
另外这个 so 里面还出现了不少这种结构的跳转,从 jump
往前分析可以看到,如果要计算最终的跳转地址,需要得到参数值,如果只是处理单个函数的这种结构的间接跳转的话,可以直接
frida hook
获取参数值获得地址,然后从地址中读值,就能计算出最后的跳转地址了,算出之后在
bn 的 mlil 层用 Set User Variable Value
的方式设置成 ConstantValue 填入计算出的固定值,bn
就能接着往下分析了
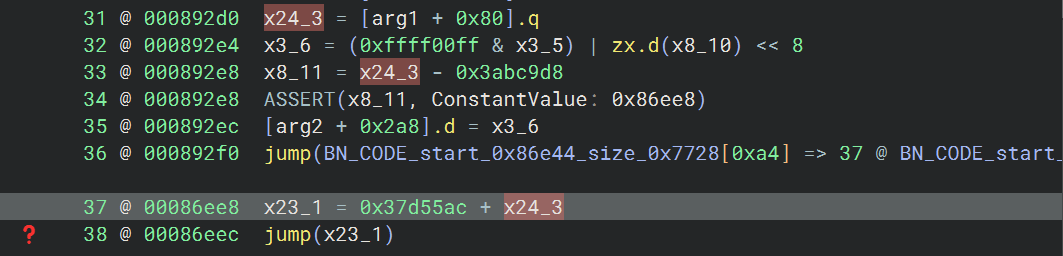
设置完之后发现又有新的跳转,并且跳转地址计算依赖于上次计算也同样涉及得到的
x24_3,那就直接给 x24_3 设置成算出的常量值
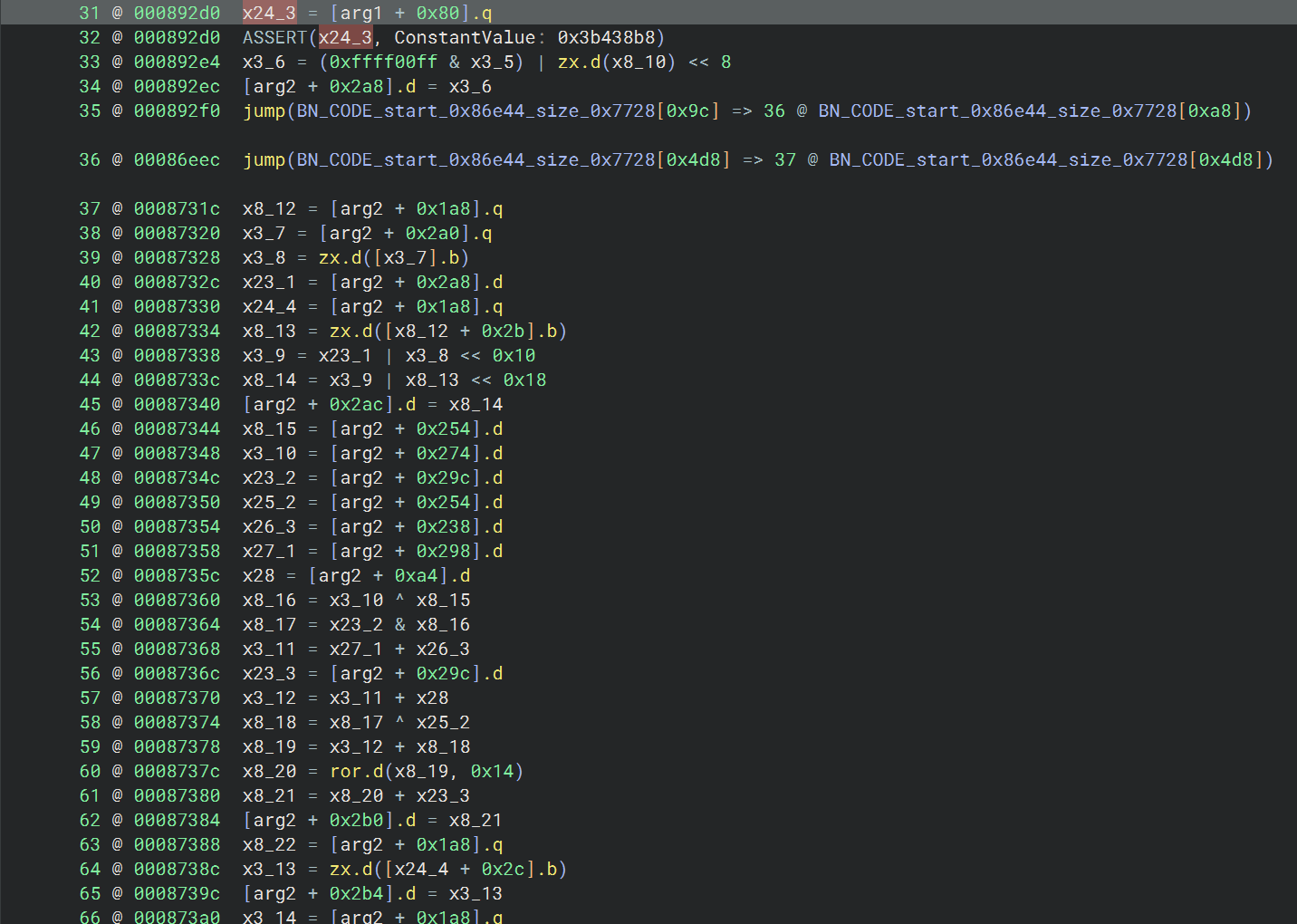
这样的话 bn 就能顺利分析下去了,并且下方出现了新的类似的跳转结构
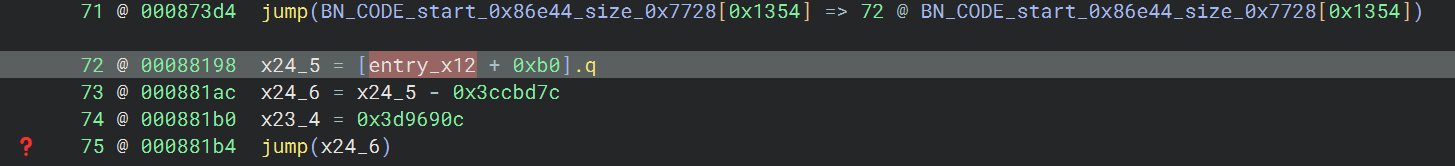
在分析的过程中发现样本中有很多都是这样的结构,每次都改 frida 脚本和手动指定值很麻烦,于是考虑自动化实现这个过程,首先在 bn 中识别出这种跳转结构,并且收集计算跳转地址和进行 frida hook 所需要的所有数据,然后自动生成 frida 脚本,执行 hook 后,再用脚本批量赋值的方式给所有这种结构的跳转设置跳转地址
识别跳转结构
从上面的分析不难看出跟最后跳转地址相关大概就三行指令
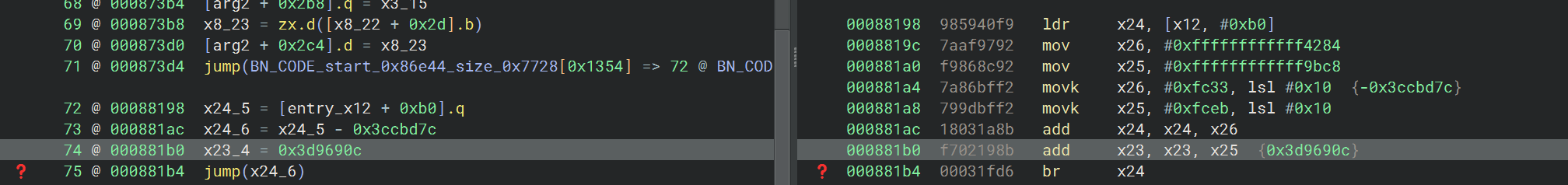
要算出最后 x24_6 的值,需要知道 x24_5
的值,并收集后面的常量值,x24_5 依赖于 x12
寄存器和